-

The most important cybersecurity habits for safe mobile banking are using the official bank app and keeping it updated, securing your login with a strong, unique password and multi-factor authentication (MFA), never conducting transactions on public Wi-Fi, and being constantly vigilant against phishing and smishing scams. As of September 2, 2025, mobile banking is the
-
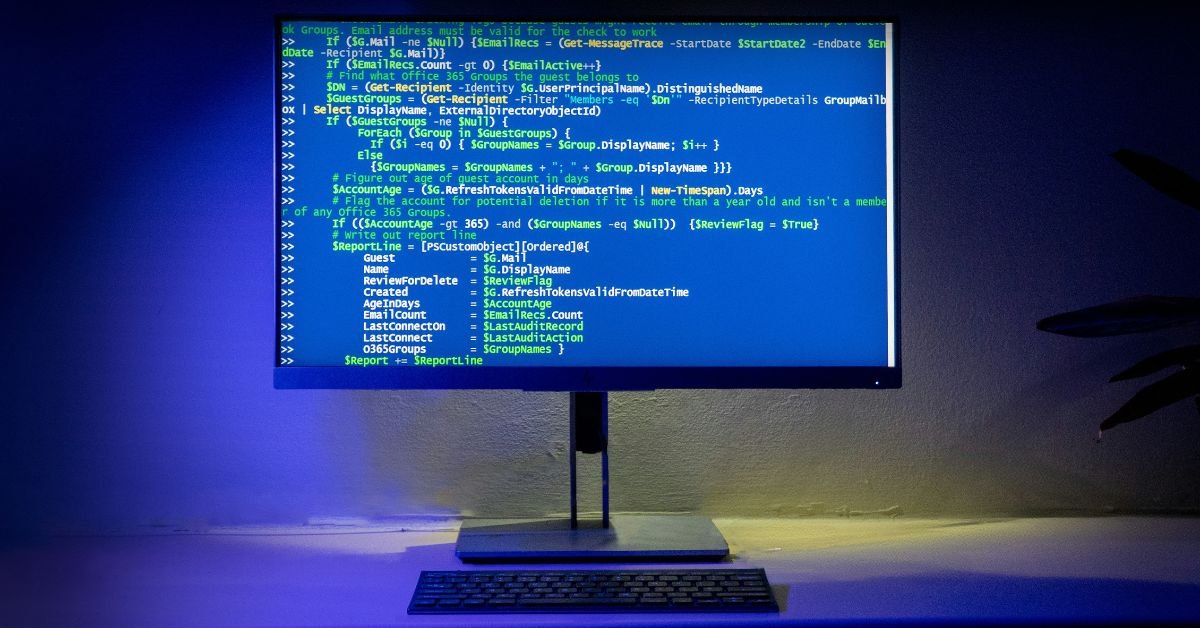
The most common cybersecurity exploits are phishing, the use of malware, the exploitation of unpatched software vulnerabilities, and web application attacks like SQL Injection (SQLi) and Cross-Site Scripting (XSS). As of September 2, 2025, these tried-and-true techniques remain the primary methods that hackers, from low-level scammers to sophisticated state-sponsored groups, use to breach defenses. For
-
Cybersecurity shapes the future of technology by moving from a reactive, “bolted-on” afterthought to a proactive, foundational element of design and innovation. As of September 2, 2025, the relentless pressure of sophisticated cyber threats and the growing global demand for data privacy are forcing a fundamental shift: technology is no longer created and then secured;